What is EtherHiding? Google flags malware with crypto-stealing code in smart contracts
North Korean hackers have adopted a method of deploying malware designed to steal crypto and sensitive information by embedding malicious code into smart contracts on public blockchain networks, according to Google’s Threat Intelligence Group.
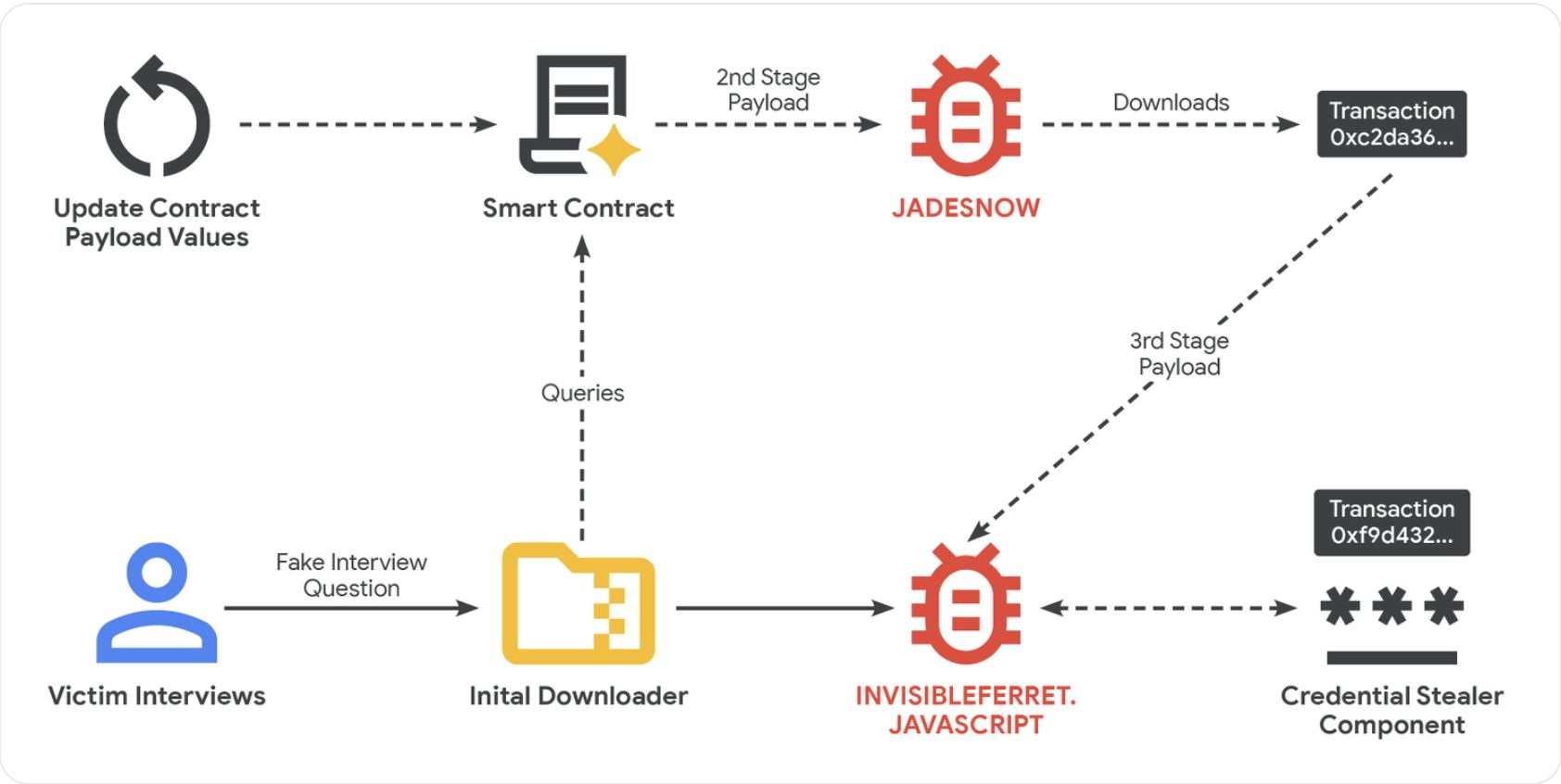
The technique, called “EtherHiding,” emerged in 2023 and is typically used in conjunction with social engineering techniques, such as reaching out to victims with fake employment offers and high-profile interviews, directing users to malicious websites or links, according to Google.
Hackers will take control of a legitimate website address through a Loader Script and embed JavaScript code into the website, triggering a separate malicious code package in a smart contract designed to steal funds and data once the user interacts with the compromised site.
The compromised website will communicate with the blockchain network using a “read-only” function that does not actually create a transaction on the ledger, allowing the threat actors to avoid detection and minimize transaction fees, Google researchers said.
The report highlights the need for vigilance in the crypto community to keep users safe from scams and hacks commonly employed by threat actors attempting to steal funds and valuable information from individuals and organizations alike.
Related: CZ’s Google account targeted by ‘government-backed’ hackers
Know the signs: North Korea social engineering campaign decoded
The threat actors will set up fake companies, recruitment agencies and profiles to target software and cryptocurrency developers with fake employment offers, according to Google.
After the initial pitch, the attackers move the communication to messaging platforms like Discord or Telegram and direct the victim to take an employment test or complete a coding task.
“The core of the attack occurs during a technical assessment phase,” Google Threat Intelligence said. During this phase, the victim is typically told to download malicious files from online code repositories like GitHub, where the malicious payload is stored.
In other instances, the attackers lure the victim into a video call, where a fake error message is displayed to the user, prompting them to download a patch to fix the error. This software patch also contains malicious code.
Once the malicious software is installed on a machine, second-stage JavaScript-based malware called “JADESNOW” is deployed to steal sensitive data.
A third stage is sometimes deployed for high-value targets, allowing the attackers long-term access to a compromised machine and other systems connected to its network, Google warned.
Magazine: Inside a 30,000 phone bot farm stealing crypto airdrops from real users
Disclaimer: The content of this article solely reflects the author's opinion and does not represent the platform in any capacity. This article is not intended to serve as a reference for making investment decisions.
You may also like
Risks and Insights from the COAI Token Fraud: A 2025 Handbook for Cryptocurrency Due Diligence and Safeguarding Investors
- COAI Token's 2025 collapse caused $116.8M losses, exposing systemic risks in algorithmic stablecoins and centralized governance. - Project's 96% supply concentration in ten wallets, opaque team identities, and weak tokenomics flagged regulatory red flags. - Global regulators froze $150M in assets but exposed jurisdictional gaps, while EU and US introduced crypto frameworks with conflicting standards. - Investors now prioritize AI audits, multi-sig wallets, and KYC compliance to mitigate risks in speculat

COAI's Unexpected Downturn in Late 2025: A Warning Story on AI Stock Valuations and Governance Risks
- COAI Index's 88% YTD drop highlights systemic risks in speculative AI equities and crypto assets amid strong AI infrastructure growth. - C3 AI's Q3 revenue growth contrasts with non-GAAP losses, underscoring AI sector's profitability challenges vs. disciplined tech peers like Benchmark Electronics. - CLARITY Act's regulatory ambiguity and EU AI Act compliance costs deter institutional investment, exacerbating COAI's governance and liquidity issues. - COAI's "fake decentralization" and C3 AI's leadership

Vanguard opens platform to Bitcoin ETFs and ends two-year blockade

3 Strong Altcoin Picks Showing Clear Growth Momentum — GIGA, ALGO, and NOT

